NetHack for Kindle
Posted by sky | Tags: Game , Linux , Open-Source , Personal , Python , Technology , installation , kindle , testing
NetHack is a single-player roguelike game. The player has to find the Amulet of Yendor at the lowest level of the dungeon to win the game.Download the NetHack binary package and extract the contents.
The NetHack control.tar.gz contains a file named postinst which is a script to be run after the binary files are installed.
The NetHack data.tar.gz extracts to the paths below under the /opt dir.
/opt/bin
/opt/share
Copy the extracted bin and share folders under the Kindle drive "local" folder.
Copy the postinst to Kindle drive.
The postinst script assumes the nethackdir to be in /opt/share/nethackdir .
For simplicity, I create a symlink for share under /opt to point to /mnt/us/local/share
Launch the myts terminal:
cd /opt mntroot rw ln -s /mnt/us/local/share share mntroot ro
Next, run the postinst script in /mnt/us
cd /mnt/us ./postinst
There is some error at the end that can be ignored.
Just type nethack (and hit
The NetHack game will display this error below:
perm_lock: Operation not permitted Cannot lock perm for unknown reason (1).
The error has to do with locking the perm file in nethackdir has failed. This is probably related to the vfat file system the perm file is residing in. The locking operation is probably not supported in vfat file system.
In the terminal, enter mount command:
mount rootfs on / type rootfs (rw) /dev/root on / type ext3 (ro,noatime,nodiratime,data=ordered) proc on /proc type proc (rw) sysfs on /sys type sysfs (rw) tmpfs on /dev type tmpfs (rw,mode=755) devpts on /dev/pts type devpts (rw,gid=5,mode=620) rwfs on /mnt/rwfs type tmpfs (rw,size=32768k) shm on /dev/shm type tmpfs (rw) rwfs on /var type tmpfs (rw,size=32768k) /dev/mmcblk0p2 on /var/local type ext3 (rw,sync,errors=continue,data=ordered) fsp on /mnt/us type fuse.fsp (rw,nosuid,nodev,noatime,user_id=0,group_id=0) /dev/loop/0 on /mnt/base-us type vfat (rw,noexec,noatime,nodiratime,fmask=0022,dmask=0022,codepage=cp437,..,..=mixed,utf8)
As can be seen from the mount command output, /dev/mmcblk0p2 partition uses ext3 file system and it is mounted at /var/local and is also writable by default.
I create a .nethack dir under /var/local , and copy the perm file in nethackdir to /var/local/.nethack
I should be able to copy all the files and subfolders in nethackdir to /var/local/.nethack and then use .nethack as the nethackdir. But, I choose to create symlinks in .nethack to point them to their original location in /mnt/us/local/share/nethackdir for all the files and subfolders.
I write a python script to do this, and place it in /mnt/us:
link.py
#!/usr/bin/python import os import sys from os import path def link_files(dir, links_dir): files = os.listdir(dir) for name in files: link = path.join(links_dir, name) if path.exists(link): continue src = path.join(dir, name) os.symlink(src, link) if __name__ == '__main__': a = sys.argv if len(a) < 3: print "link.py src_dir links_dir" sys.exit(0) link_files(a[1], a[2])
As Duokan contains Python 2.6 binary in DK_System\xKindle\python, I just create a symlink in /usr/bin to link to it.
cd /usr/bin mntroot rw ln -s /mnt/us/DK_System/xKindle/python/bin/python python mntroot ro cd /mnt/us python link.py /mnt/us/local/share/nethackdir /var/local/.nethack
Because the perm file is already placed in /var/local/.nethack previously, the python script will not create a symlink for it. So, essentially, the perm file is in the ext3 file system, and the rest of nethack files are in the Kindle drive vfat file system.
Last step is to modify the nethack script in /mnt/us/local/bin/nethack (Change/addition is highlighted)
#!/bin/sh
# SCCS Id: @(#)nethack.sh 3.4 1990/02/26
TERMINFO=/usr/share/terminfo/
export TERMINFO
HACKDIR=/opt/share/nethackdir
export HACKDIR
HACK=$HACKDIR/nethack
MAXNROFPLAYERS=4
# cm
NETHACKDIR=/var/local/.nethack
export NETHACKDIR
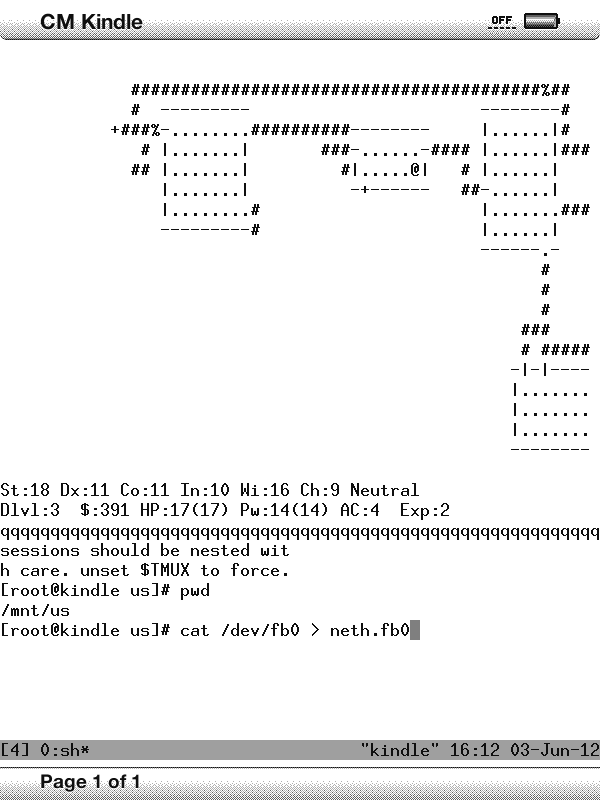
Finally, nethack runs! :)
Also, I downloaded the Gnugo package.
For gnugo, only gnugo (under /opt/bin) needs to be copied to Kindle drive local/bin.
Related:
Linux Apps for Kindle